BİLGEM
E-ID Technologies

National Identity Card / TR & TRNC Identity Card
- Electronic ID Card Application
- Electronic Travel Document Application
- Visual authentication:
Photograph, wet signature, guilloche, rainbow print, MLI, micro text, raster print, charm, relief print, optical variable ink, ultraviolet ink and OVD/DOVID - Electronic authentication:
Electronic certificate, digital photo, PIN - Biometric verification:
Fingerprint, finger vein print, hand palm print - Ability to upload Qualified Electronic Certificate (QC) and private key
- ISO/IEC 7816-3 compliant contact communication
- ISO/IEC 7816-4, 8, 9 compliant instruction set
- AES-256 secure messaging
- Get hashes (SHA-1, SHA-256, SHA-384, SHA-512)6
- Card Verifiable Certificate (CVC) support
- Role-based access control mechanism
- True Random Number Generator (TRNG)
- RSA digital signing, decryption and certificate validation1
- Generating RSA key pair2
- ECDSA signing (ECC 128 – 640 bit range)3
- ECC key pair generation (ECC 128 – 640 bit range)3
- Symmetric encryption/decryption (DES3, AES-128, AES-192, AES-256)3
- Cryptographic integrity calculation (DES3 MAC/CMAC/RetailMAC, AES MAC/CMAC)3
- Common Criteria (CC) EAL 4+ security level
- Multi-chip support4
- UKTUM-H v7.01
- Infineon SLE78CFX2400P
- NXP P71D320P, P71D352B
- Standards compliance
- ICAO 9303
- ISO/IEC 14443-3, 4 compliant contactless communication
- ISO/IEC 7816-4, 8, 9 compliant instruction set
- ICAO Technical Report Supplemental Access Control for MRTDs
- BSI TR-03110 (for EAC)
- BSI TR 03111
- Compatible with ICAO LDS 1.7 data structure
- Basic Access Control (BAC)
- Active Authentication (AA)
- RSA (up to 2048 bit): SHA-1, SHA-256, SHA-384, SHA-512
- ECC (up to 521 bit): SHA-1, SHA-224, SHA-256, SHA-384, SHA-512
- Supplemental Access Control (SAC)
- PACE v2
- MRZ and CAN support
- Generic Mapping and Integrated Mapping support
- ECDH (Brainpool curves up to 512 bits)
- DH (1024 bits, 2048 bits)
- Extended Access Control (EAC)
- EAC v1 (CA v1, TA v1)
- RSA (up to 3072 bit): SHA-1, SHA-256, SHA-512
- ECC (up to 521 bit): SHA-1, SHA-224, SHA-256, SHA-384, SHA-512
- Contactless Communication
- ISO/IEC 14443-3, 4 Type-A
- 424/848 kbps communication speed
- Secure Communication
- DES3
- AES-128, AES-192, AES-256
- Common Criteria (CC) security level
- CC EAL 4+ for BAC (ALC_DVS.2)
- CC EAL 5+ for SAC & EAC (ALC_DVS.2, AVA_VAN.5)
- Multi-chip support7
- Infineon SLE78CLFX3000P, SLE78CLFX4000P, SLE78CLFX308AP, SLE78CLFX408AP
- NXP P71D320P
[1] RSA 1024 – 2816 bit range is supported for AKiS v2.5, only RSA 1024 and 2048 bits are supported for AKiS v2.2.
[2] RSA 1024 – 2816 bit range is supported for AKiS v2.5, only RSA 2048 bit is supported for AKiS v2.2.
[3] Only supported in AKiS v2.5.
[4] Chips have at least CC EAL 5+ security assessment certification.
[5] These are the features of AKiS TRAVEL.
[6] Only SHA-1 and SHA-256 are supported for AKiS v2.2.
[7] Chips have at least CC EAL 6+ security assessment certification.
GGM - Embedded Security Module
- Product information
- Technicial Features
The Embedded Security Module has been developed to be used in security applications such as secure storage of passwords, access control and authentication on tablet computers, mobile phones and similar devices. The security module, which uses the UKTUM-Hv7.0 integrated circuit with the common criterion EAL5+ security level, constitutes a reliable national option in terms of functionality, performance and price.
The Embedded Security Module, which is used in the production of tablet computers with its QFN type cover, implements the authentication function that allows only authorized persons to access the data stored on the tablet computer.
- Microprocessor: based on 8051 (Internal memory: 256 B)
- Flash memory: Total 192 Kb
- 64 Kb ROM and 128 Kb data memory or
- It can be defined as 128 Kb ROM and 64 Kb data memory.
- SRAM: 8Kb
- Interface: Compliant with ISO/IEC 7816 standard
- Hardware crypto support resistant to side-channel analysis:
- DES and 3-DES coprocessor
- AES256 coprocessor
- RSA1024 and RSA2048 coprocessor
- RSU: Physical random number generator that generates real random numbers in accordance with the FIBS-140-2 standard
- Security: Common Criteria EAL5+ certification
- Safety sensors: High-low supply voltage/clock frequency/temperature detection
- Protection of the IC surface against attacks with an effective shield
- Detecting laser and bug attacks
- Precautions against side channel analyzes


AKIS PKI
- Product information
- Technicial Features
AKiS operating system has been developed in accordance with ISO/IEC 7816 standards and has PKI features. AKİS v2.2, v2.5 and v2.6 versions can be used in user login (login), digital signature and similar PKCS#11 applications if they are customized with PKCS#15 data structure.
- ISO/IEC 7816-3 compliant contact communication
- ISO/IEC 7816-4, 8, 9 compliant instruction set
- AES-256 secure messaging
- Get hashes (SHA-1, SHA-256, SHA-384, SHA-512)8
- Card Verifiable Certificate (CVC) support2
- Role-based access mechanism
- True Random Number Generator (TRNG)
- RSA digital signing and decryption operations2
- Generating RSA key pair3
- ECDSA signing (ECC 128 – 640 bit range)4
- ECC key pair generation (ECC 128 – 640 bit range)4
- Cryptographic integrity calculation (DES3 MAC/CMAC/RetailMAC, AES MAC/CMAC)4
- Symmetric encryption/decryption (DES3, AES-128, AES-192, AES-256 : CBC, ECB, GCM)5
- WRAP / UNWRAP Key6
- ECDH Key Derivation6
- Session based Symmetric Key generation6
- Session based ECC Key Pair generation6
- Common Criteria (CC) EAL 4+ security level
- Multi-chip support7
- UKTUM-H v7.01
- Infineon SLE78CFX2400P
- NXP P71D320P, P71D352P
1Driver support for PKCS#11 applications (PKCS#11 and Minidriver).
2RSA 1024 – 2816 bit range is supported for AKiS v2.5 and RSA 1024 – 2688 bit range for AKiS v2.6, only RSA 1024 bits and 2048 bits are supported for AKiS v2.2.
3RSA 1024 – 2816 bit range is supported for AKiS v2.5 and RSA 1024 – 2688 bit range is supported for AKiS v2.6, only RSA 2048 bit is supported for AKiS v2.2.
4 Supported in AKiS v2.5 and v2.6.
5Supported in AKiS v2.5 and v2.6; CBC and ECB modes are supported in v2.5 and v2.6, while GCM (Galois Counter Mode) mode is only supported in v2.6.
6Only supported in AKiS v2.6.
7The chips have at least CC EAL 5+ security assessment certification.
8Only SHA-1 and SHA-256 are supported for AKiS v2.2.
AKİS GEZGİN E-Passport
- Product information
- Technicial Features
AKiS GEZGiN E-Passport application has been developed in accordance with ICAO 9303 standards. Thanks to the Basic Access Control (BAC) and Supplemental Access Control (SAC) features, the information on the contactless chip can only be read with secure communication, and the passport is prevented from being copied thanks to the Active Authentication feature. In addition, with the EAC feature, personal biometric data is protected by using CVC certificates, only authorized countries can access this data.
Logical Data Structure (LDS) 1.7 is supported in AKiS GEZGiN E-Passport application and there can be a maximum of 11 data groups1 (DG1–DG11). Of these, the identification of DG1 with MRZ data is mandatory, while the identification of other data sets is optional.1 data group (DG1 – DG11) can be found. Of these, the identification of DG1 with MRZ data is mandatory, while the identification of other data sets is optional.
1 More data groups can be defined in AKiS GEZGiN v2.0.
- Active Authentication (AA)RSA (up to 2560 bits)6: SHA-1, SHA-256, SHA-384, SHA-512
- ECC (up to 521 bit): SHA-1, SHA-224, SHA-256, SHA-384, SHA-512
- PACE v2
- MRZ, CAN and PIN2 support
- Generic Mapping and Integrated Mapping support
- ECDH (Brainpool curves up to 512 bits)
- DH (1024 bits, 2048 bits)
- EAC v1 (CA v1, TA v1)3
- RSA (up to 3072 bit): SHA-1, SHA-256, SHA-512
- ECC (up to 521 bit): SHA-1, SHA-224, SHA-256, SHA-384, SHA-512
- ISO/IEC 14443-3, 4 Type A
- 424/848 kbps communication speed
- DES3
- AES-128, AES-192, AES-256
- CC EAL 4+ for BAC (ALC_DVS.2)
- CC EAL 5+ for SAC & EAC (ALC_DVS.2, AVA_VAN.5)
- Infineon SLE78CLFX3000P, SLE78CLFX308AP, SL78CLFX4000P and SLE78CLFX408AP
- NXP P71D320P and P71D352P5
- ICAO 9303
- ISO/IEC 14443-3, 4
- ISO/IEC 7816-4, 8, 9
- ICAO Technical Report Supplemental Access Control for MRTDs
- BSI TR-03110 (for EAC)
- BSI TR 03111
BASIC ACCESS CONTROL (BAC)
It is the mechanism that provides access to the data in the contactless chip by an authorized terminal and ensures that the messaging between the terminal and the contactless chip is done securely. It enables the generation and verification of session keys and initiation of secure messaging by optically reading the MRZ (Machine Readable Zone) or CAN (Card Access Number) information printed on the e-Passport.
EXTENDED ACCESS CONTROL (EAC)
It enables to update secure session keys with Chip Authentication (EAC – CA) and to control access to biometric data groups (DG3: fingerprint, DG4: iris) in the chip by using role-based certificates with Terminal Authentication (EAC – TA).
ACTIVE AUTHENTICATION
It prevents making an exact copy of the e-Passport chip.
SUPPLEMENTAL ACCESS CONTROL (SAC)
It is a mechanism that enables the creation of more secure and stronger session keys than BAC, thanks to Diffie - Hellman key generation protocols (DH/ECDH).
2 PIN support is available in AKiS GEZGiN v2.0.
3 A maximum of 32 roles can be used in AKiS GEZGiN v2.0.
4 The chips have CC EAL 6+ security evaluation certification.
5 Compatible with AKiS GEZGiN v2.0.
6 For AKiS GEZGiN v1.x, RSA is supported up to 2048 bits.

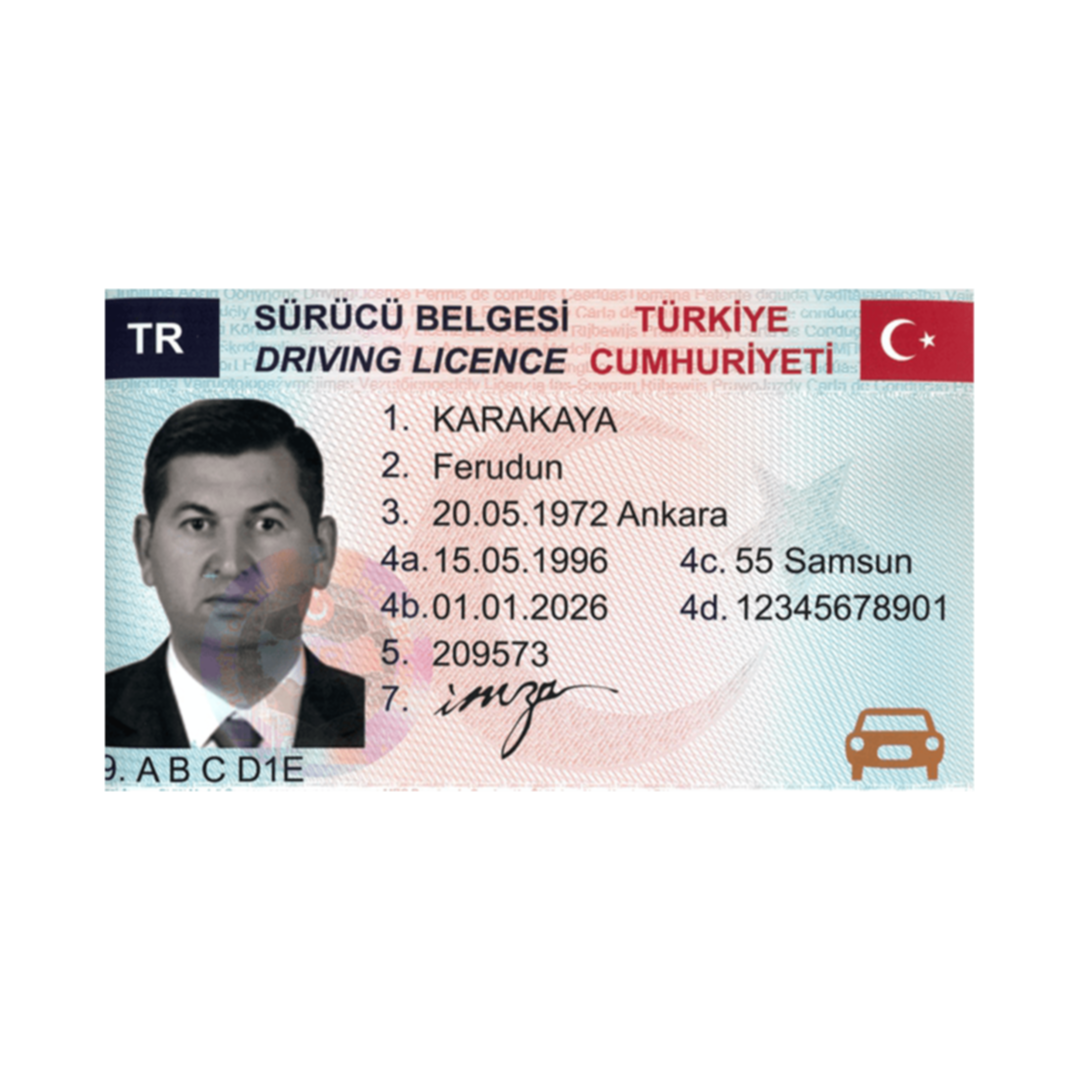
AKİS GEZGİN E-Driver's License
- Product information
- Technicial Features
AKiS GEZGiN E-Driver's Licence application has been developed in compliance with ISO/IEC 18013 standards (ISO/IEC 18013-3:2009 and ISO/IEC 18013-3:2017)1 . Thanks to the Basic Access Protection (BAP) feature, the information on the contactless chip can only be read with secure communication, and the Active Duplication feature prevents the driver's licence from being copied. Extended Access Protection (EAP) feature (ISO/IEC 18013-3:2009 compliance) protects all files (DG1 - DG24) and Extended Access Control (EAC) feature (ISO/IEC 18013-3:2017 compliance) protects personalised biometric data files (DG7 and DG8). EAP/EAC ensures that only authorised readers can access these data groups.
In the application of AKiS GEZGiN E-Driver's License, a total of 24 data groups (DG1 – DG24) can be found for ISO/IEC 18013-3:2009 compliance, and a total of 14 data groups (DG1 – DG14) for ISO/IEC 18013-3:2017 compliance; The definition of DG1, which includes the demographic data of the document holder and the vehicle category, restrictions and conditions, is mandatory, while the definition of other data groups is optional.2
1 Personalized AKiS GEZGiN cards can only support one of the ISO/IEC 18013-3:2009 and ISO/IEC 18013-3:2017 standards, depending on customization.
2More data groups can be defined in AKiS GEZGiN v2.0.
- RSA (up to 2560 bits)7: SHA-1, SHA-256, SHA-384, SHA-512
- ECC (up to 521 bit): SHA-1, SHA-224, SHA-256, SHA-384, SHA-512
- ISO/IEC 18013-3:2009
- RSA (up to 3072 bit): SHA-1, SHA-256, SHA-512
- ECC (up to 521 bit): SHA-1, SHA-224, SHA-256, SHA-384, SHA-512
- PACE v2
- MRZ, SAI and PIN3 support
- Generic Mapping support
- ECDH (Brainpool curves up to 512 bits)
- ISO/IEC 18013-3:2017
- EAC v14
- ECC (up to 521 bit): SHA-1, SHA-224, SHA-256, SHA-384, SHA-512
- ISO/IEC 14443-3, 4 Type-A
- 424/848 kbps communication speed
- DES3
- AES-128, AES-192, AES-256
- CC EAL 4+ (ALC_DVS.2) for BAP Config 1
- CC EAL 5+ for SAC & EAC (ALC_DVS.2, AVA_VAN.5)
- Infineon SLE78CLFX3000P, SLE78CLFX308AP, SLE78CLFX4000P, SLE78CLFX408AP
- NXP P71D320P, P71D352P 6
- ISO/IEC 18013-3
- ISO/IEC 14443-3, 4
- ISO/IEC 7816-4, 8, 9
- BSI TR-03110 (for EAC)
- BSI TR 03111
BASIC ACCESS PROTECTION (BAP)
It is the mechanism that provides access to the data in the contactless chip by an authorized terminal and ensures that the messaging between the terminal and the contactless chip is done securely. It enables the generation and verification of session keys and initiation of secure messaging by optically reading the SAI (Scanning Area Identifier) information printed on the E-Driver's License or entering it by the operator.
EXTENDED ACCESS PROTECTION (EAP)
It enables to update secure session keys with Chip Authentication (EAP - CA) and to control access to all data groups in the chip by using role-based certificates with Terminal Authentication (EAP - TA).
EXTENDED ACCESS CONTROL (EAC)
It allows updating secure session keys with Chip Authentication (EAC – CA) and controlling access to optional signature and biometric data groups in the chip using role-based certificates with Terminal Authentication (EAC – TA).
ACTIVE AUTHENTICATION
It prevents making an exact copy of the e-Driving License chip.
SUPPLEMENTAL ACCESS CONTROL (SAC)
It is a mechanism that enables the creation of more secure and stronger session keys than BAC, thanks to Diffie - Hellman key generation protocols (DH/ECDH).
3 PIN support is available in AKiS GEZGiN v2.0.
4A maximum of 32 roles can be used in AKiS GEZGiN v2.0.
5 Valid for AKiS GEZGiN v2.0.
6 The chips have CC EAL 6+ security evaluation certification.
7 For AKiS GEZGiN v1.x, RSA is supported up to 2048 bits.
AKIS TICKET
- Product information
- Technicial Features
AKiS Ticket is a CIPURSE1 based, contactless smart card product running on the Smart Card Operating System (AKIS) developed nationally by TÜBİTAK BİLGEM, a member of the OSPT Alliance. AKiS TICKET is designed to be used as a payment tool in electronic fare collection systems, especially in the field of transportation, due to the advanced security infrastructure it provides and the open standards it is based on. It is also the first domestic smart card solution in contactless card applications such as access authorization control and parking systems.
1 CIPURSE open specifications are published by the OSPT Alliance.
KEY FEATURES
- Contactless data rate up to 848 kbps
- 13.56MHz operating frequency
- ISO / IEC 14443-4 compliant
- ISO/IEC 7816 compliant file system
- ISO / IEC 7816-4 and ISO/IEC 7816-9 compliant APDU instruction set2
- 8 app support2
- Support for 32 files per application2
- Binary File, Linear Record Type, Rotary Record Type, Value Record Type Files
- Consistent Transaction mechanism3
- Multiple App support
SAFETY FEATURES
- Hardware platform with CC EAL 6+ security level
- True Random Number Generator (TRNG)
- AES-1284, 128-bit forward encryption mechanism
- 8 AES-128 security keys for each application
- Flexible key management structure
- Built-in protection mechanism against Differential Power Analysis (DPA) attacks
- Built-in protection mechanism against Differential Fault Analysis (DFA) attacks
- ISO / IEC 9798-2 based Mutual Authentication (Mutual Authentication, AES-128)
- Secure Messaging modes based on ISO/IEC 7816-4 (Plain, AES MACed, AES ENCed)
- Data integrity protection
- File-based Access Authorization and Secure Messaging
SCOPE OF APPLICATION
- E-Ticket applications
- Personnel attendance control systems
- Access authorization control systems
- Parking systems
- Libraries
- Health, welfare, loyalty, etc. card apps
CIPURSE OPEN STANDARDS
CIPURSE open standards provide a proven technology infrastructure built on ISO/IEC 7816, ISO/IEC 14443 standards and AES-128 to provide secure, flexible and standardized electronic toll collection solutions.
INDEPENDENT TECHNOLOGY
Platform independent: CIPURSE technology can be implemented on any smart card chip that meets all specifications, as well as an applet on NFC SIM cards or JavaCards.
Supplier independent: CIPURSE technology was developed not as a specific manufacturer's solution, but as a standard and open technology that anyone can implement. Today, many companies, including TÜBİTAK, produce CIPURSE products and the number of these companies is increasing.
Card reader standalone: No changes are required in existing card readers in order to communicate with CIPURSE cards. CIPURSE technology can be used in all smart card readers that comply with ISO/IEC 14443 Type A L4 standards.
2 Applies to CIPURSE T Profile only.
3 A mechanism that prevents possible data corruption that may occur in communication problems by ensuring that the data to be written to the card is written at once and completely.
4 AES, Advance Encryption Standard, ISO / IEC 18033-3:2010 & FIPS 197.


KYS - Card Management System
- Product information
- Technicial Features
KYS is a set of applications that can manage the entire life cycle of identity cards, driver's licenses, passports and similar documents.
Due to its modular structure, KYS can offer solutions suitable for different needs. Different solutions can be produced according to the needs of the institution from the inventory, reporting, personalization and registration modules in the KYS.
KYS has safely met the needs of many medium and large-scale organizations until today.
- Server: Independent of platform and database management system. It easily integrates into external systems with web-services. It provides role-authorization-based access and redundancy support and implements all business logic in the customization process.
- Smart Card: Compatible with National Smart Card Operating System (AKIS) and JCOP. It has integration with identity, passport and driver's license applications.
- Security: It has the features of authorization-based access, secure storage of sensitive data, SSL connection between terminals, electronic signed transaction records and card access to the system.
- PKI: Works integrated with the National Public Key Infrastructure (MA3).
- Role-based authorization
PERSONALIZATION
- Creating an application package
- Application package management
- Application package personalization
- Quality control
- Integration with industrial and desktop customization machines
- Chip coding with contact and contactless interfaces of cards
- Terminal and user management
- Announcement management
REGISTRATION
- Application registration
- Card and application status tracking
- Mobile (online/offline) application registration
- Obtaining biometric registration in accordance with standards
REPORTING
- Card based reporting
- Machine based reporting
- Reporting by transaction records
- Parametric query options
- Ability to produce output in PDF, MS Excel and MS Word formats
INVENTORY
- Serial numbered / unnumbered card entries can be made
- Card return, cancellation and destruction processes
- Distributing cards in the personalization environment
- End of day transactions
- Safe pickup and delivery
- Card status summary notification
EKDS - Electronic Authentication System
- Product information
- Features
While performing the service, it confirms whether the people who participate in the service and want to benefit from the service are really the people they claim.
ELECTRONIC AUTHENTICATION SYSTEM COMPONENTS
ELECTRONIC ID CARD
It is a smart identity card used for personal identity verification in order to benefit from the services offered by public service institutions.
CARD ACCESS DEVICE
The Card Access Device (KEC) is one of the terminal devices of EKDS and is used to verify that the ID card is issued by the authorized institution for applications that serve in the electronic environment and that the card really belongs to the holder.
AUTHENTICATION SERVER
It is the server where the authenticity of the authentication notifications created by KEC is checked.
AUTHENTICATION POLICY SERVER
The authentication process is carried out in accordance with the policies determined by each institution depending on the services it offers. While some institutions find only the card password (PIN) sufficient, some institutions may request verification with both the card password and biometrics. Institutions' authentication policies are defined on this server.
INTERFACE APPLICATION SOFTWARE
The integration of the software used by the institutions into EKDS is carried out through interface application software. Interface applications can be a desktop application [Automation Software Interface (OYA/WIA)] or an application running on a server [Security Services Platform (GSP)].
AUTHENTICATION FACTORS
- Physical verification
- Secure messaging
- Electronic certificate
- Password (PIN code)
- Biometrics
- Digital photography


GEM - Secure Access Module
- Product information
- Technicial Features
GEM is the security module of the Card Access Device (it performs the cryptographic operations of the Card Access Device), which is designed to be able to validate the Turkish ID card and electronically verify the cardholder for applications serving in the electronic environment. By means of GEM, data fields such as the biometric data of the card holder can be accessed and read/written in these fields. In addition, by using the certificates and keys in GEM, secure communication is made with the Turkish identity card. In short, GEM is a module that enables citizens to use the Card Access Device securely and thus to have their identity information verified electronically in a secure manner.
- Communicate with ISO 7816 (contact) standard message sets
- ISO 7816 instruction set support
- Secure messaging
- Symmetric and asymmetric encryption methods (3DES, RSA, AES)
- Original file and memory management system
- Structured security architecture and security key management
- Role-based access
- PKCS11, CSP support
- Has CC EAL4+ security certification
- Compatible with UKTUM, Infineon and NXP chips