BİLGEM
Secure Communication
MILSEC-4 Secure IP Communication System
- Product information
- Security Features
- Technicial Features
While the MİLSEC-4 terminal offers an up-to-date solution for new generation secure communication (voice, data and video) in IP networks, it also provides an uninterrupted communication service by maintaining the compatibility of secure voice communication in PSTN networks with PSTN secure phones in use.
Key/certificate distribution, surveillance and software update processes of MILSEC-4 terminals are carried out securely remotely using the Security Management Center (GYM). MİLSEC-4 terminal has the ability to update keys/certificates remotely by using IP network through secure communication with GYM.
MİLSEC-4 terminals are interoperable with the MİLSEC-1A phone and offer the opportunity to replace MİLSEC-1A phones without interruption in the communication network during the gradual transformation of PSTN networks to next generation IP networks.
- Crypto initialization key
- National and NATO crypto algorithms
- NATO SCIP compliance
- Hardware red-black separation
- Remote secure software update
- Remote secure certificate and key update
- COMSEC, TEMPEST, EMI/EMC approvals
- CONFIDENTIAL level communication by connecting directly to the Internet network
- IP and/or PSTN connection
- Commercial SIP products open voice communication
- Interoperability with the MILSEC-1A safety phone
- MİLSEC-4’ler arası güvenli ses ve görüntülü haberleşme
- Secure data and instant communication
- Secure voice call with secure PTSN phone

MİLSEC 3 - National Radio Sound Safety Device
- Product information
- Security Features
- Environmental Conditions
RELIABLE SOLUTIONS FOR TACTICAL COMMUNICATION
MİLSEC-3 is a secure communication device that can transmit voice and data encrypted and half-duplex over HF/VHF/UHF radio lines. Thanks to its flexible interface, it can work in harmony with many voice, data and radio devices. It is equivalent to NATO KY58 and KY100 devices in terms of its physical properties and connections, and can be used in all kinds of military platforms such as aircraft, helicopters, ships, ground stations. While communicating with other MİLSEC-3 devices in national mode using the national crypto algorithm, it can also make encrypted calls with KY58 and KY100 devices thanks to the NATO crypto algorithm it contains.
- National and NATO crypto modes
- Ability to keep crypto keys without erasing for up to 60 days thanks to the built-in battery
- Anahtarların silinmiş olduğu durumda “Hizmete Özel” gizlilik dereceli ses görüşmesi yapılabilmesi için “Acil Yedek” modu
- TEMPEST and crypto approvals
- St : MIL-STD-810E, Method 516.4
- Temperature shock: MIL-STD-810E, Method 503.3
- Vibration: MIL-STD-810F, Method 514.5
- Gun shot vibration: MIL-STD-810F, Method 519.5
- Height: MIL-STD-810F, Method 500.4
- Humidity: MIL-STD-810E, Method 507.3
- Salt fog : MIL-STD-810F, Method 509.4
- Acceleration: MIL-STD-810F, Method 513.5
- Solar radiation : MIL-STD-810F, Method 505.4
- Sprinkling: MIL-STD-810F, Method 506.4
- Powder : MIL-STD-810F, Method 510.4
- Explosive atmosphere : MIL-STD-810F, Method 511.4
- EMC approval
IPKC-T - Tactical IP Crypto Device
- Product information
- Security Features
- Technicial Features
SECURE COMMUNICATION ON TACTICAL IP NETWORKS
IPKC-T provides network layer security for traffic between IP local area networks communicating over insecure networks. Since the device is designed to be portable, easy to use, small in size, low power consumption and resistant to environmental conditions, it is capable of meeting the security needs of both single and medium-sized IP networks in tactical field land, sea and air vehicles. The device connects between the local area network and the router and creates a security gateway. The device is capable of processing data up to a total speed of 220 Mbit/s.
- Data security with "CONFIDENTIAL" level of confidentiality
- Authentication
- Data integrity
- Tamper-proof, emergency-erase switch
- Hardware-based implementation
- Hardware-based true random number generator
- Hardware red-black separation
- Encryption: Certified National Encryption Algorithm
- Authentication: Certified National Authentication Algorithm
- Key exchange: ECDH
- Signing: ECDSA
- Automatic key exchange with IKE Protocol
- X.509 Certificate based operation
- Two-stage, role-based device access control with smart-card and password
- Smart-card-based Crypto Initialization Key and User Card
- Recording of event, alarm, transaction information
- Offline key upload in MILAY mode with key upload device
- Online key upload via IP Key Management Center and EKADAS
- Secure communication of IP/Ethernet networks over unsecured unprotected networks
- High speed data transmission from one point to many points at the same time in the network structure
- Performance: 110 Mbps full-duplex (220 Mbps combined)
- 512 tunnels
- IPv4, IPv6, TCP, UDP, ICMP, SNMP, FTP
- 2 x 10/100/1,000 Mbit/s Gigabit Ethernet (IEEE 802.3), autosense, autocrossover
- Command-based configuration with local management (console) port, user-friendly command set
- Remote management by SNMP-based IP Management Center
- Local and remote (Management Center) configuration backup / refresh
- VRRP support for redundancy
- Time synchronization with NTP
- Software update locally and remotely via IP Management Center
- Communication with IPKC-G2 and IPKC-GX belonging to the same family
- COMSEC, EMI/EMC and TEMPEST

IPKC-GX - 10 Gigabit IP Crypto Device
- Product information
- Security Features
- Technicial Features
10 SECURE COMMUNICATION OVER GIGABIT NETWORKS
IPKC-GX secures the traffic between IP local area networks that communicate over insecure networks at the network layer. The device connects between the local area network and the router and creates a security gateway. It provides data privacy, authentication, data integrity security services. The device is capable of meeting the security needs of IP networks in cloud and data centers that require very high performance.
- Data security with "CONFIDENTIAL" level of confidentiality
- Authentication
- Data integrity
- Tamper-proof, emergency-erase switch
- Hardware-based implementation
- Hardware-based true random number generator
- Hardware red-black separation
- Encryption: Certified National Encryption Algorithm
- Authentication: Certified National Authentication Algorithm
- Key exchange: ECDH
- Signing: ECDSA
- Automatic key exchange with IKE protocol
- X.509 Certificate based operation
- Two-stage, role-based device access control with smart-card and password
- Smart-card-based Crypto Initialization Key and User Card
- Recording of event, alarm, transaction information
- Offline key upload in MILAY mode with key upload device
- Online key upload via IP Key Management Center and EKADAS
- Secure communication of IP/Ethernet networks over unsecured unprotected networks
- High speed data transmission from one point to many points at the same time in the network structure
- Performance: 9 Gbps full-duplex (18 Gbps combined)
- 8,000 tunnels
- IPv4, IPv6, TCP, UDP, ICMP, SNMP, FTP
- 2x 10 GbE (10 Gigabit Ethernet) Copper or Fiber
- Command-based configuration with local management (console) port, user-friendly command set
- Remote management by SNMP-based IP Management Center
- Local and remote (Management Center) configuration backup / refresh
- VRRP support for redundancy
- Time synchronization with NTP
- Software update locally and remotely via IP Management Center
- Communication with IPKC-G2 and IPKC-T belonging to the same family
- COMSEC, EMI/EMC and TEMPEST
IPKC-G2 - Gigabit IP Crypto Device
- Product information
- Security Features
- Technicial Features
SECURE COMMUNICATION VIA GIGABIT NETWORKS
IPKC-G2 secures traffic between IP local area networks communicating over insecure networks at the network layer. The device connects between the local area network and the router and creates a security gateway. It provides data privacy, authentication, data integrity security services. The device is capable of processing data up to a total speed of 1.8 Gbit/s.
- Data security with "CONFIDENTIAL" level of confidentiality
- Authentication
- Data integrity
- Tamper-proof, emergency-erase switch
- Hardware-based implementation
- Hardware-based true random number generator
- Hardware red-black separation
- Encryption: Certified National Encryption Algorithm
- Authentication: Certified National Authentication Algorithm
- Key exchange: ECDH
- Signing: ECDSA
- Automatic key exchange with IKE protocol
- X.509 Certificate based operation
- Two-stage, role-based device access control with smart-card and password
- Smart-card-based Crypto Initialization Key and User Card
- Recording of event, alarm, transaction information
- Offline key upload in MILAY mode with key upload device
- Online key upload via IP Key Management Center and EKADAS
- Secure communication of IP/Ethernet networks over unsecured unprotected networks
- High speed data transmission from one point to many points at the same time in the network structure
- Performance: 900 Mbps full-duplex (1.8 Gbps combined)
- 2,000 tunnels
- IPv4, IPv6, TCP, UDP, ICMP, SNMP, FTP
- 2 x 10/100/1,000 Mbit/s Gigabit Ethernet (IEEE 802.3), auto sense, auto crossover
- Command-based configuration with local management (console) port, user-friendly command set
- Remote management by SNMP-based IP Management Center
- Local and remote (Management Center) configuration backup / refresh
- VRRP support for redundancy
- Time synchronization with NTP
- Software update locally and remotely via IP Management Center
- Communication with IPKC-T and IPKC-GX belonging to the same family
- COMSEC, EMI/EMC and TEMPEST

AGC-T - Tactical Network Security Device
- Product information
- Security Features
- Technicial Features
SECURE COMMUNICATION OVER IP NETWORKS
AGC-T; taktik saha IP ağlarının güvenli biçimde haberleşebilmesini sağlayan, son teknoloji ürünü, düşük güç tüketimine sahip bir cihazdır. Cihaz; taşınabilir, kullanımı kolay, küçük ebatlı ve saha çevresel şartlarına dayanıklı olarak tasarlanmıştır. AGC-T, farklı konumlardaki taktik saha IP ağlarının, güvensiz ağlar üzerinden güvenli biçimde haberleşebilmesini sağlar. Cihaz korunmak istenen yerel ağ ile yönlendirici arasına bağlanır ve bu ağı güvensiz ağdan yalıtan bir geçit işlevi görür. AGC-T 220 Mbps’e kadar trafik işleme yeteneğine sahiptir.
- Data privacy at the "CONFIDENTIAL" level of confidentiality
- Authentication
- Data integrity
- Tamper-proof, emergency-erase switch
- Hardware-based implementation
- Hardware-based random number generator
- Hardware red-black separation
- A set of encryption and authentication algorithms certified at confidential confidentiality level
- Key exchange: ECDH
- Signing: ECDSA
- Automatic key exchange with IKE protocol
- X.509 Certificate-based operation (operational security, easy key management)
- Two-stage device access control with smart-card and password
- Administrator, authorized, unauthorized operator user level
- Smart card based Crypto Initialization Key and User Card
- Recording of Events, Alarms, Transaction information
- Smart card based offline key upload
- Online key upload via IP Key Management Center and EKADAS
- Secure communication service over insecure networks
- Simultaneous point-to-multipoint communication
- Performance: 110 Mbps full-duplex (220 Mbps combined)
- 512 tunnels
- IPv4, IPv6, TCP, UDP, ICMP, SNMP, FTP
- 2 x 10/100/1,000 Mbit/s Gigabit Ethernet (IEEE 802.3), autosense, autocrossover
- Command-based configuration with local management (console) port, user-friendly command set
- Remote management by SNMP-based IP Management Center
- Local and remote (Management Center) configuration backup / refresh
- VRRP (Active-Passive Redundancy)
- Time synchronization with NTP
- Local and remote (Management Center) software update
- Communication with AGC-G and AGC-GX belonging to the same family
- COMSEC, EMI/EMC and TEMPEST
AGC-G - Gigabit Network Security Device
- Product information
- Security Features
- Technicial Features
SECURE COMMUNICATION THROUGH GIGABIT NETWORKS
AGC-G provides security at the network layer of traffic between IP local area networks that communicate over insecure networks. The device connects between the local area network and the router and creates a security gateway. It provides data privacy, authentication, data integrity security services. The device is capable of processing data up to a total speed of 1.8 Gbit/s.
- Data privacy at the "CONFIDENTIAL" level of confidentiality
- Authentication
- Data integrity
- Tamper-proof, emergency-erase switch
- Hardware-based implementation
- Hardware-based random number generator
- Hardware red-black separation
- A set of encryption and authentication algorithms certified at confidential confidentiality level
- Key exchange: ECDH
- Signing: ECDSA
- Automatic key exchange with IKE protocol
- X.509 Certificate-based operation (operational security, easy key management)
- Two-stage device access control with smart-card and password
- Administrator, authorized, unauthorized operator user level
- Smart card based Crypto Initialization Key and User Card
- Recording of events, alarms, transaction information
- Smart card based offline key upload
- Online key upload via IP Key Management Center and EKADAS
- Secure communication of IP/Ethernet networks over unsecured unprotected networks
- Gigabit data transmission from one point to many points at the same time in the network structure
- Performance: 900 Mbps full-duplex (1.8 Gbps combined)
- 2,000 tunnels
- IPv4, IPv6, TCP, UDP, ICMP, SNMP, FTP
- 2 x 10/100/1,000 Mbit/s gigabit ethernet (IEEE 802.3), auto sense, auto crossover
- Command-based configuration with local management (console) port, user-friendly command set
- Remote management by SNMP-based Security Management Center
- Local and remote (Management Center) configuration backup / refresh
- VRRP (active-passive redundancy)
- Time synchronization with NTP
- Software update locally and via Management Center
- Communication with AGC-T and AGC-GX belonging to the same family
- COMSEC, EMI/EMC and TEMPEST capability


AGC-GX - 10 Gigabit Network Security Device
- Product information
- Security Features
- Technicial Features
10 SECURE COMMUNICATION OVER GIGABIT NETWORKS
AGC-GX provides security at the network layer of traffic between IP local area networks that communicate over insecure networks. The device connects between the local area network and the router and creates a security gateway. It provides data privacy, authentication, data integrity security services. The device is capable of meeting the security needs of IP networks in cloud and data centers that require very high performance.
- Data security with "CONFIDENTIAL" level of confidentiality
- Authentication
- Data integrity
- Tamper-proof, emergency-erase switch
- Hardware-based implementation
- Hardware-based true random number generator
- Hardware red-black separation
- A set of encryption and authentication algorithms certified at confidential confidentiality level
- Key exchange: ECDH
- Signing: ECDSA
- Automatic key exchange with IKE protocol
- X.509 Certificate based operation
- Two-stage, role-based device access control with smart-card and password
- Smart-card-based Crypto Initialization Key and User Card
- Recording of event, alarm, transaction information
- Smart card based offline key upload
- Online key upload via IP Key Management Center and EKADAS
- Secure communication of IP/Ethernet networks over unsecured unprotected networks
- High speed data transmission from one point to many points at the same time in the network structure
- Performance: 9 Gbps full-duplex (18 Gbps combined)
- 8,000 tunnels
- IPv4, IPv6, TCP, UDP, ICMP, SNMP, FTP
- 2 x 10 GbE (10 Gigabit Ethernet) Copper or Fiber
- Command-based configuration with local management (console) port, user-friendly command set
- Remote management by SNMP-based IP Management Center
- Local and remote (Management Center) configuration backup / refresh
- VRRP support for redundancy
- Time synchronization with NTP
- Software update locally and remotely via IP Management Center
- Communication with AGC-G and AGC-T belonging to the same family
- COMSEC, EMI/EMC and TEMPEST
FASD-1 - Fax Analog Digital Converter
- Product information
- Security Features
- Technicial Features
FAX SECURITY SOLUTIONS
With the FASD-1, which provides the opportunity to encrypt PC-based fax communication, it is possible to prevent the combination of red-black information existing in currently used faxes and to add AMSG-720B TEMPEST feature to fax communication. FASD-1 is UEKAE's low-cost solution for secure fax communication.
- Ability to connect any crypto device conforming to RS-232 standard, 19,200/38,400 asynchronous N-8-1 protocol
- Ability to encrypt faxes (fax without interface) that do not require crypto interface, working according to T.30 protocol
- RJ-11 socket input to connect the telephone line
- RJ-11 socket input to connect fax device
- Data rates of 14,400, 9,600, 7,200, 4,800, and 2,400 bits/s
- Compliance with MIL-STD-461E standard
- Compliance with NATO SDIP 27/A TEMPEST standard

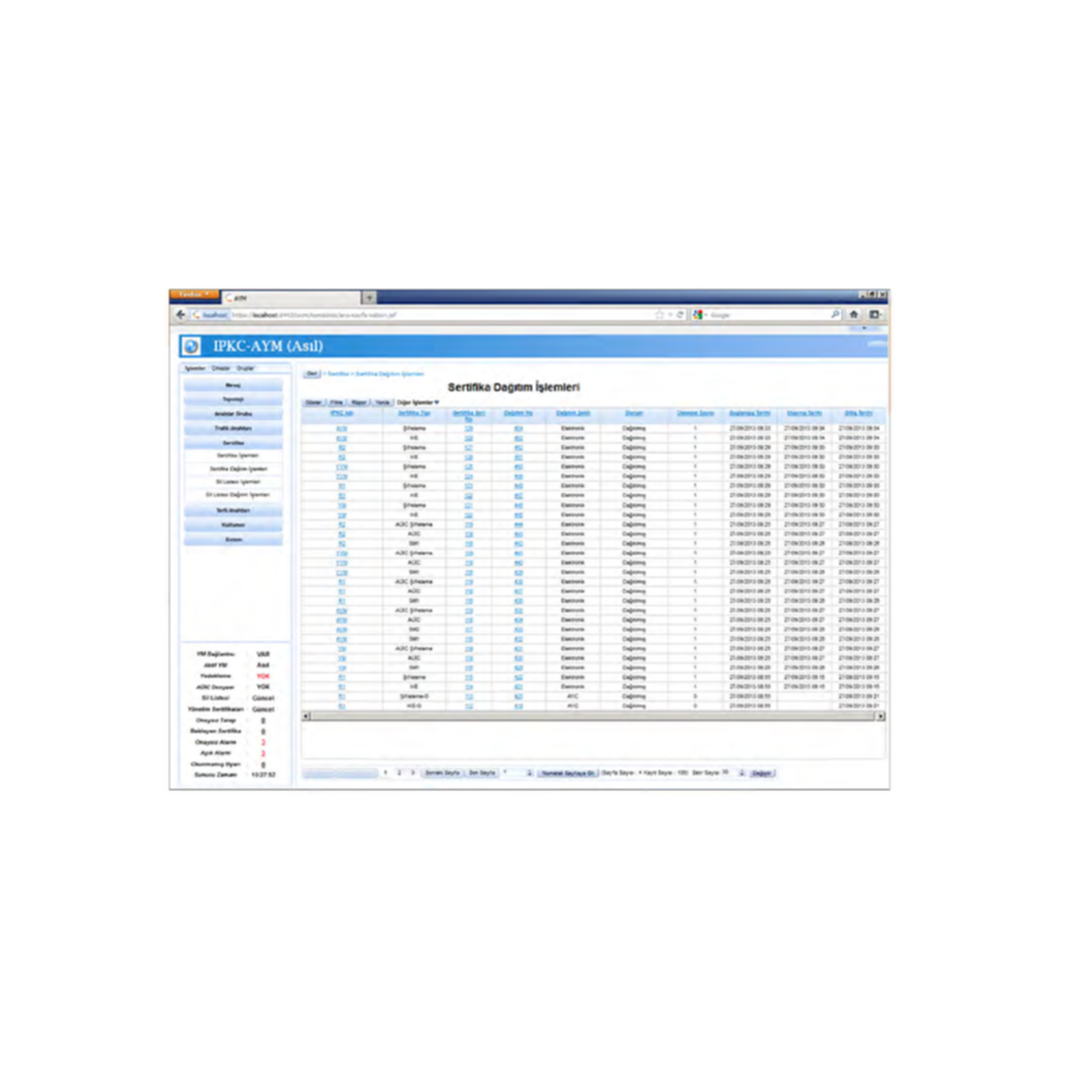
IP-AYM - IP Key Management Center
- Product information
- Features
IP-GYM KEY MANAGEMENT CENTER
IP-AYM Key Management Center performs central key management of IPKC/AGC devices. IP-AYM works in harmony with IP-YM. IPKC/AGC's symmetric and asymmetric (certificate) keys are managed by IP-AYM. IPKC/AGC AYM works integrated with AU&İC (Key Generation and Processing Device) or EKADAS Key Management Infrastructure for key generation works. It includes distribution, accounting and management functions. It is designed on the basis of 24/7 operation and geographical and physical backup is possible. The user interface is web-based and the system can be managed from the desired secure point. Since it is designed in application architecture, it has an infrastructure suitable for expansion.
- Key generation by AU&IC
- Key distribution
- Key accounting
- Key destruction
- Certificate production (with AU&IC)
- Online certificate distribution
- Certificate accounting
- Certificate Revocation List (CRL) management
- Key alarm monitoring
- Key alarm configuration
- User creation, deletion and update operations
- Dynamic role management
- Smart card based user identification
- User and system logs
- Geographical and physical backup
IP-YM - IP Crypto Management Center
- Product information
- Features
- Security Features
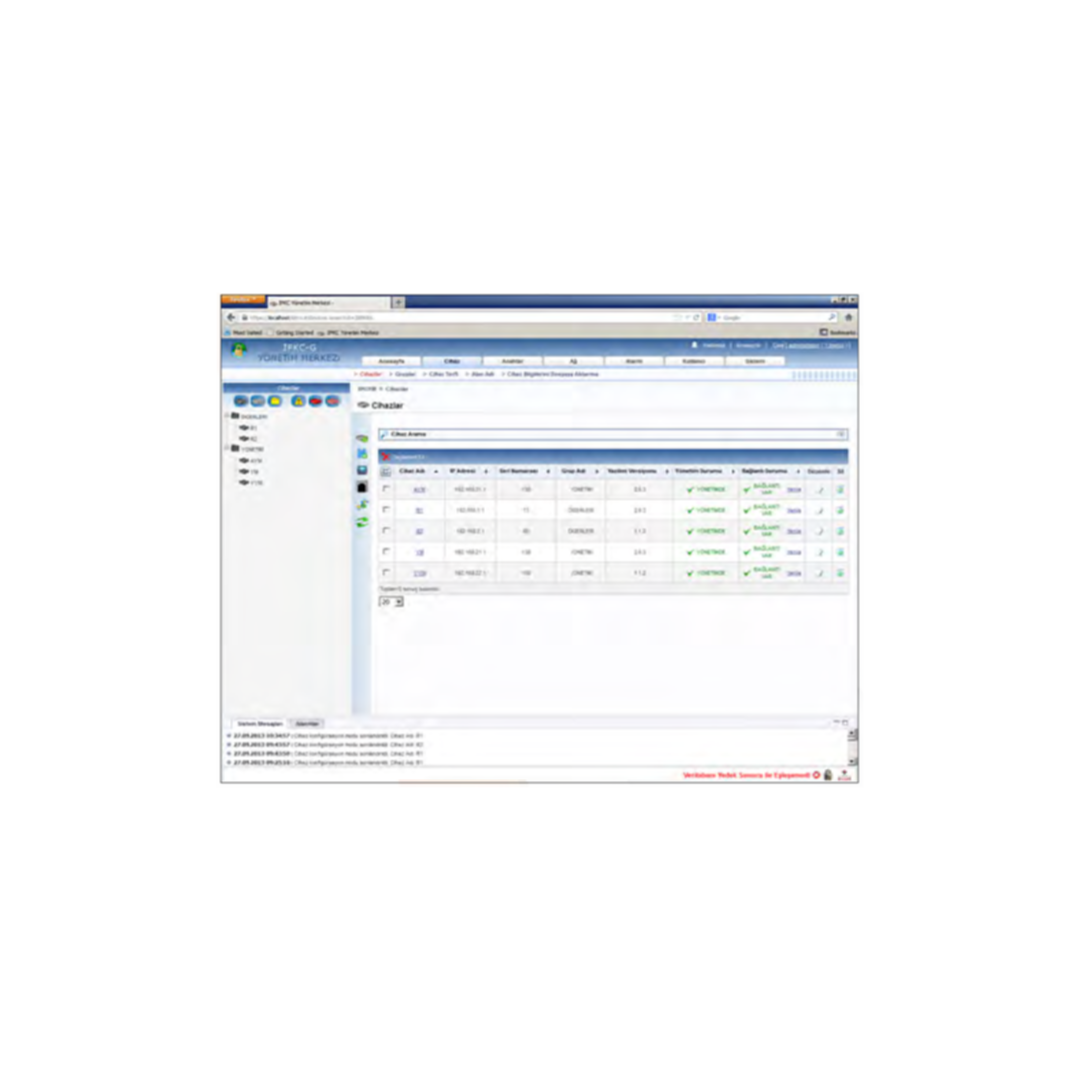
IPKC/AGC Management Center is a server-based system with a web user interface that enables centralized management of IPKC/AGC IP crypto devices. It ensures that the configuration, alarm and logs of the devices can be managed centrally and securely. The IPKC/AGC Management Center has advanced features that enable network administrators to easily perform management activities.
- Single point management of devices
- Multiple browser support
- Advanced AJAX-based user interface
- Client-server architecture
- Multiple user support
- Role and permission based user management
- Customizable role creation
- Configurable log and report generation
- Online key upload with Key Management Center software
- Online backup
- E-mail alert
- Throughput monitoring with device performance management
- Graphical monitoring of device MIB counters
- Alarm management and reporting
- Built-in Syslog support and device log management
- Built-in FTP server
- Geographical and physical backup
- Smart card based authentication
- Role-based user authorization
- SSLv3
- SNMPv3
- Use of IPKC/AGC assigned to management communication
- Hierarchical grouping of devices
- Display of managed devices and groups in tree structure
- Periodic device connection check
- Automatic device recognition and management
- Ability to test inter-device connectivity
- Optional device date and time configuration
- Detailed IPSec configuration management
- Device IPSec configuration error checking and reporting
- IPSec tunnel monitoring
- Remote firmware update
- Device configuration backup and restore
- Key group creation
- Device network configuration
- Device network elements management
- Device local user management